Federal spending records indicate the U.S. Embassy in Beijing purchased internet service from China Unicom, a state-owned firm banned in the United States for national security reasons, and concerns over espionage.
Records indicate the sensitive White House communications during President Trump’s state visit to China, as well as ongoing State Department communications with the Biden White House may also be compromised, The National Pulse can reveal.
White House Compromised?
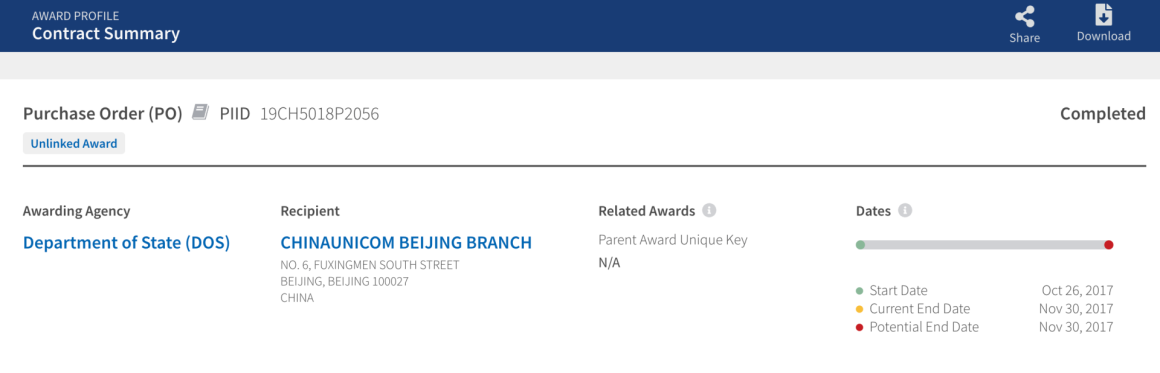
On October 26, 2017, a contract for “WHCA data and phone lines” was awarded to China Unicom Beijing Branch. WHCA is the acronym for the White House Communications Agency. The funding agency for this contract is listed as the Defense Information Systems Agency. The description listed on another contract dated the following day reads, “Beijing POTUS WHCA data and voice lines.” That is, “Beijing President of the United States White House Communications Agency (WHCA) Data and Voice Lines.” A third contract for WHCA data and phone lines was awarded November 1, 2017.
These contracts are significant because just days after, on November 8-10, 2017, President Trump visited Beijing on an official state visit. Indeed the contracts appear to be directly linked to Trump’s tenure as President, beginning just after he was inaugurated, and ending soon after he left office, suggesting the man and his communications were the target of Chinese spying, aided by State Department apparatchiks.
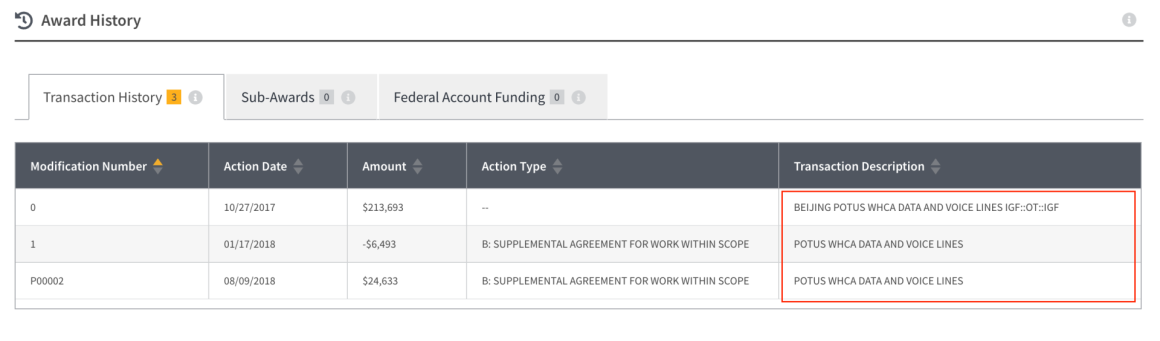
Following this, a contract was awarded to China Unicom (2019) for an “OpenNet P2P circuit” between Beijing and the White House. OpenNet is a “Sensitive But Unclassified (SBU) network” operated by the State Department for email and data applications. Another such contract was made in late 2021 for a connection between Beijing and the Biden White House.
In the early days of the coronavirus outbreak, contracts (2019 and 2020) were awarded to China Unicom for upgrades to the State Department’s OpenNet communications network and internet service in Wuhan. The State Department also maintains a consulate in Wuhan.
China Unicom – or the China United Network Communications Group Co., Ltd – was founded in the early 1990s by the Chinese Communist Party (CCP). To this day, China Unicom’s key figures are also high ranking members of the CCP’s party committee and political leadership.
In 2020, the Guardian newspaper reported: “China appears to have used mobile phone networks in the Caribbean to surveil US mobile phone subscribers as part of its espionage campaign against Americans, according to a mobile network security expert who has analysed sensitive signals data.”
Around the same time, authorities in the U.S. were attempting to restrict the reach of China Unicom inside the United States, including the company being named by the Department of Defense as part of an investigation into the “People’s Republic of China’s (PRC) Military-Civil Fusion development strategy, which supports the modernization goals of the People’s Liberation Army (PLA) by ensuring its access to advanced technologies and expertise acquired and developed by even those PRC companies, universities, and research programs that appear to be civilian entities.”
The Federal Communications Commission finally “banned” China Unicom in 2022.
Who’s Responsible?
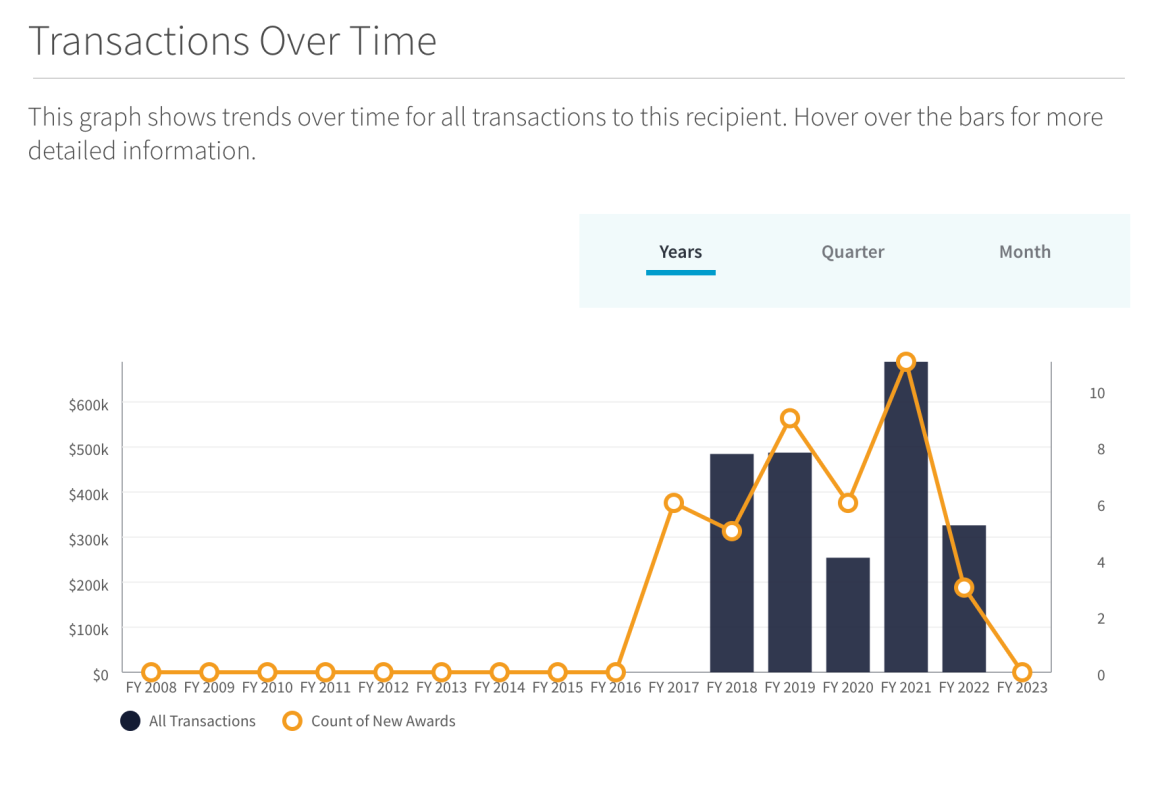
Despite its recent activities, the U.S. State Department took part in some 60 transactions totalling over $2.5 million to China Unicom between 2017 and 2023. The federal spending database also lists China Unicom, a state-owned enterprise, as a “minority-owned business”.
In previous reporting, the National Pulse revealed Nick Burns, the current U.S. Ambassador to China, worked at a CCP-linked consulting firm, and a Harvard group advising China’s military. Another National Pulse story revealed Ambassador Burns headlining an event sponsored by the U.S.-China Heartland Association (USCHA), a Chinese Communist Party-linked foreign influence group targeting American farmers and farmland.
Burns’s predecessor, former Governor of Iowa Terry Branstad, first met Xi Jinping in 1985 and has referred to the communist dictator as an “old friend.” Since leaving his post as ambassador, Branstad has formed a consulting group geared toward businesses and organizations looking to do business in China and the United States.
Sanctions Upon Sanctions.
On June 17, 2020, the Committee for the Assessment of Foreign Participation in the United States Telecommunications Services Sector recommended to the FCC that an application from a company called Pacific Light Cable Network for an undersea cable link between Hong Kong and the United State be denied.The recommendation was based partly on the company’s “relationship with PRC intelligence and security services” and for its “connections to PRC state-owned carrier China Unicom.”
On August 28, 2020, the Defense Department added China Unicom to a list of “Communist Chinese Military Companies” operating in the United States.
Following this action, President Trump issued an executive order on November 12, 2020 “Addressing the Threat from Securities Investments that Finance Communist Chinese Military Companies.”
On December 8, 2020, the State Department issued a fact sheet entitled, “U.S. Investors Are Funding Malign PRC Companies on Major Indices,” which listed China Unicom as one of those malign companies, even though their own embassy in Beijing was utilizing their services.
On January 7, 2021, China Unicom was delisted by the New York Stock Exchange following President Trump’s executive order.
A State Department fact sheet issued on January 14, 2021, again discussed the threat posed by China Unicom, among other PRC companies.
President Biden revised President Trump’s executive order on June 3, 2021, however China Unicom remained under restriction after the revision.
On December 16, 2021, the Department of Treasury’s Office of Foreign Assets Control released an updated list of Chinese Military-Industrial Complex Companies, which continued to designate China Unicom as such.
On January 27, 2022, the Federal Communications Commission (FCC) revoked China Unicom’s authority to provide telecom services in the United States.
On September 20, 2022, the FCC added China Unicom to the “List of Equipment and Services Covered by Section 2 of The Secure Networks Act.” The release stated that China Unicom is “subject to the exploitation, influence and control of the Chinese government, and the national security risks associated with such exploitation, influence, and control.”
The FCC document goes on to state that the DOJ, DOD, and Executive Branch all concur that services provided by China Unicom “involve communications services that pose ‘an unacceptable risk to the national security of the United States or the security and safety of United States persons’ under section 2 of the Secure Networks Act—thus requiring the addition of these services to the Covered List.”
The FCC public notice furthermore states:
“With respect to China Unicom, the Executive Branch entities found that the United States national security environment, including increased concern about malicious cyber activities taken at the direction of the Government of the PRC, has changed significantly since 2002, when the Commission certified the international section 214 authorization of China Unicom to provide international common carrier services; that China Unicom’s status as a wholly-owned subsidiary of a PRC state-owned enterprise firmly places it under the exploitation, control, and influence of the Chinese government; that China Unicom has continuing and ongoing commercial relationships with Chinese entities accused of engaging in activities contrary to American national security and economic interests; and that China Unicom’s American operations provide opportunity to facilitate Chinese cyber activities including economic espionage, disruption and misrouting of American communications traffic, and access to U.S. records and other sensitive data. Accordingly, based on these findings, the Executive Branch entities have determined that services provided by China Unicom associated with its international section 214 authorization pose a substantial and unacceptable risks to the national security of the United States and its people.”
And yet, just three months later, despite all of these very explicit warnings, and contrary to U.S. Government sanctions, the State Department signed another contract with China Unicom on December 27, 2022 for “OpenNet P2P circuit between BJ and WH 2023.” That is a communications link between Beijing and the White House.
Beijing Rules.
When the United States began building a new embassy in Moscow in 1979, they used Soviet workers and materials for construction. In 1985, construction was halted. The partially-completed American embassy in Moscow was found to be so compromised by electronic surveillance devices that it was dubbed “the bug house.” Recommendations were made to tear it down and start over. Ultimately, part of the building was torn down and construction was completed years later, using American-supplied materials and workers.
Now, the government is once again contracting foreign technical assistance for something they should be able to do themselves and is essentially paying an enemy intelligence service to bug their embassy.
One would think that the United States Government would have sufficient technology to install their own secure internet service using encrypted satellites, without relying on a CCP-owned company that has been banned in the homeland as an espionage threat. One would also think that such an arrangement should be immediately undone and that any potential compromise of our systems in Beijing and elsewhere in China should be investigated forthwith by the relevant counterintelligence agencies.
Even if the networks in question were encrypted, an ISP can glean useful metadata for cyber targeting. The National Pulse recently reported that the Defense Department has been purchasing vulnerable Chinese network equipment for use on sensitive bases.
During the Cold War, the CIA developed what it called “The Moscow Rules,” referring to the tradecraft needed to navigate the dangerous environment clandestine operatives faced in the Soviet capital. Perhaps a set of “Beijing Rules” should be developed as well. One basic and obvious rule should be not to hire the CCP to install your internet service.